The Vendor Sprawl Problem No One Talks About Honestly

Picture the technology vendor list that a typical mid-sized enterprise has accumulated over the past decade. There is a specialist for API management, a different one for data observability, another for identity management, one for contract lifecycle management, one for log aggregation, one for load testing, and a separate one for penetration testing. Each was the right decision at the time. Each solved a real problem. And together, they have created something no one planned for: a vendor portfolio that is itself a full-time job to manage.
This is vendor sprawl. It is not a failure of procurement. It is the natural result of a "best-of-breed for every problem" philosophy applied consistently over a long period. The problem is not that any individual vendor is bad. The problem is what happens when you multiply them together: procurement overhead, contract negotiation cycles, integration maintenance, security audit fatigue, and the invisible coordination tax that comes from having your critical business logic spread across a dozen different SaaS dashboards.
Most technology leaders know this is a problem. Fewer have a principled framework for deciding what to do about it. The answer is not "consolidate everything" and it is not "keep specializing forever." The answer, as usual, is more nuanced - and the nuance matters a lot when the wrong decision costs millions.

What Vendor Sprawl Actually Costs
Before talking about solutions, it is worth being precise about the costs. The obvious ones show up on the balance sheet: license fees multiplied by vendor count, often with overlapping capabilities you are paying for twice. A 2023 analysis by Productiv found that enterprises with 500+ employees have an average of 473 SaaS applications deployed, and that roughly 45% of licenses in a typical portfolio go unused in any given month. If your annual SaaS spend is $2 million, you may be wasting $900,000 on licenses that nobody opens.
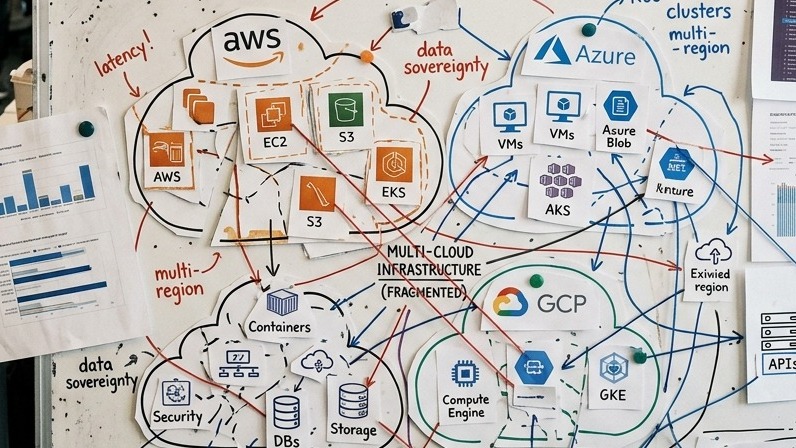
But the hidden costs are often larger. Consider the integration tax: every point-to-point integration between two vendor systems requires initial development, ongoing maintenance, and a team member who understands the specifics when something breaks at 2am. At 20 vendors with an average of 3 integrations each, you are maintaining 60 integration points. Each one is a potential failure mode, a security surface, and a source of latency in your data flows.
Then there is the security audit burden. Most regulated industries require annual security reviews of third-party vendors. At 20 vendors, that is 20 questionnaire cycles, 20 sets of SOC 2 reports to review, and 20 renewal negotiations where the vendor knows switching costs are high. The direct time cost is significant. The opportunity cost - senior engineers doing vendor compliance work instead of building products - is often larger.
Finally, there is what we call architectural coherence debt. When your core business logic is distributed across a dozen vendor platforms, each with its own data model, API conventions, and failure modes, the mental model required to understand your own system becomes overwhelming. Onboarding new engineers takes longer. Root cause analysis during incidents is harder. Decisions about system evolution require vendor-by-vendor impact assessment. The complexity compounds.
When Consolidation Makes Sense - and When It Does Not
Consolidation is not always the right answer. There are domains where specialization genuinely wins, and forcing consolidation into a generalist platform creates more problems than it solves. Understanding the distinction is critical before you start renegotiating contracts.
Consolidation makes sense when: The vendors in question serve adjacent or overlapping functions that a full-stack partner can deliver with genuine quality parity. Your integration overhead between vendors is high relative to the marginal benefit of each vendor's specialization. The switching cost of consolidation is lower than the compounding operational cost of maintaining the sprawl. Your organization has a strategic relationship with one vendor who can invest in understanding your specific domain requirements over time.
Specialization wins when: You are in a domain with genuine depth requirements - financial risk modeling, genomics data processing, satellite imagery analysis - where the best-of-breed vendor's capability advantage over a generalist is large and consequential. The integration overhead is low because the specialized tool operates largely independently. Your team has deep expertise in evaluating and managing that specific class of tool. The regulatory environment requires specialized vendor certifications that generalists cannot obtain.
The error most organizations make is treating this as a binary choice. In practice, the right architecture is a tiered vendor portfolio: a small number of strategic full-stack partners who own large domains, supplemented by a small number of genuine specialists for capabilities that are both critical and differentiated. The goal is not zero vendors. The goal is a vendor portfolio small enough to manage strategically and coherent enough to operate efficiently.
An Evaluation Framework for Consolidation Decisions
When evaluating whether to consolidate a set of vendors, we recommend scoring each vendor relationship across four dimensions before making any decisions.
Strategic alignment: Does this vendor's roadmap align with where your business is going? A vendor who is deeply invested in the capabilities you will need in three years is worth more than one who solves your current problem perfectly but is stagnating. Ask vendors directly: "What is the largest investment you are making in the next 18 months, and why?" The answer tells you a lot about whether they will still be the right choice when your needs evolve.
Integration surface: How many of your other systems does this vendor touch? High-integration vendors carry disproportionate coordination overhead. A vendor who sits at the center of many data flows is a consolidation candidate because their removal would also remove multiple integration points. A vendor who operates in isolation is a consolidation candidate for a different reason: they can often be replaced without ripple effects.
Capability substitutability: Could a qualified generalist partner deliver 90% of this vendor's value? For most infrastructure and development tooling categories, the honest answer is yes. For specialized analytics, security research, or domain-specific AI, the answer is often no. Be rigorous here - your attachment to a particular vendor's UX is not the same as genuine capability differentiation.
Total cost of ownership: Do not compare license fees. Compare total cost of ownership across the full lifecycle: procurement, integration, training, ongoing support, security audit, and eventual migration. A vendor with lower license fees but high integration complexity and poor documentation may cost more than a more expensive vendor whose integration is trivial and whose support is responsive.

Total Cost of Ownership: The Full Picture
When technology leaders run vendor consolidation numbers, they typically undercount on both sides. They undercount the true cost of the current sprawl (missing integration maintenance, incident response time, and compliance overhead), and they undercount the one-time cost of consolidation (migration effort, parallel operation period, retraining, and productivity loss during transition).
A more accurate TCO model for a consolidation decision should include: current annual license costs across all affected vendors; estimated annual engineering hours spent on integration maintenance at fully-loaded cost; annual compliance and security audit overhead; one-time migration cost including data migration, integration rebuilding, and testing; productivity loss during transition (typically 15-25% of team capacity for 2-4 months on a well-managed consolidation); and the ongoing cost savings from reduced complexity, typically realized 6-12 months post-transition.
In our experience working with clients who have executed consolidations, the break-even point on a well-scoped consolidation typically falls between 14 and 20 months. Projects where the break-even exceeds 24 months should be scrutinized carefully - the savings may be real, but the organizational disruption of a long transition often undermine the business case.

Strategic Partnership Models: What Good Looks Like
The alternative to vendor sprawl is not a single-vendor dependency. It is a strategic partnership model built around a small number of deeply capable partners who are accountable for outcomes, not just deliverables.
The key difference between a vendor relationship and a strategic partnership is context. A vendor sells you a product and supports you in using it. A strategic partner invests in understanding your business well enough to make proactive recommendations, identifies capability gaps before they become problems, and has enough context about your architecture and goals to deliver coherent solutions rather than isolated features.
This kind of relationship requires investment from both sides. From the partner: deep domain expertise, proactive communication, and genuine accountability for outcomes. From the client: willingness to share strategic context, provide timely feedback, and engage with the partner as a long-term collaborator rather than a transactional supplier.
The organizations that benefit most from consolidated vendor relationships are those that treat their primary technology partner the way they would treat a senior internal hire: investing in onboarding them to the business context, giving them appropriate access to information, and holding them accountable for results while giving them the autonomy to execute effectively.
Transition Planning: The Execution Matters as Much as the Decision
A consolidation decision that is correct in principle can still fail in execution. The most common failure modes are predictable and avoidable.
Parallel operation periods that go on too long. Running old and new systems in parallel is necessary for risk management, but every week of parallel operation is a week your team is maintaining two systems instead of one. Define hard deadlines for cutover from the start, and treat slippage as a risk indicator rather than a scheduling inconvenience.
Underestimating the data migration complexity. Data migrations are almost always harder than they look. The schema differences between systems are rarely the hard part. The hard part is the data quality issues, the edge cases that only appear at scale, and the downstream systems that depended on specific data formats from the old vendor. Build in explicit time for data validation and reconciliation - at minimum, 30% of the total migration timeline.
Neglecting the human transition. Your team has institutional knowledge of the old vendors' quirks, limitations, and workarounds. That knowledge does not transfer automatically to the new system. Structured training and a transition period where team members operate new systems under guidance is not optional overhead - it is what determines whether the efficiency gains from consolidation are actually realized.

Where GTEMAS Fits In
GTEMAS operates as a full-stack engineering partner across product development, infrastructure, security, data engineering, and QA. For clients managing vendor sprawl across these domains, we offer a consolidation alternative: a single partner with deep capability across the stack, accountable for coherent delivery rather than isolated services.
This is not a pitch for consolidating everything into GTEMAS. There are capabilities where specialist vendors will always be the right choice, and we work alongside them. What we offer is coverage of the broad engineering domains where the marginal value of specialization is low and the coordination overhead of managing multiple vendors is high.
If your organization is evaluating vendor consolidation and wants a frank assessment of where consolidation creates value versus where specialization is genuinely worth the overhead, we are happy to work through it with you.
