The Perimeter That No Longer Exists
For most of the history of enterprise network security, the mental model was simple: there is an inside and an outside, and your job is to keep the bad things on the outside. You built a firewall, you issued VPN credentials, and anything that got through the perimeter was considered trusted. The castle-and-moat analogy was apt, and for a period when your users sat at desks inside office buildings connecting to servers in an on-premise data center, it worked reasonably well.
That model is not broken. It is obsolete. The conditions that made it work no longer exist for most organizations. Your users are connecting from home networks, hotels, and airports. Your workloads run in AWS, GCP, and Azure. Your business-critical applications are SaaS products hosted by vendors who may have their own vendor dependencies you have never audited. The "inside" of your network is now everywhere and nowhere simultaneously.
The consequences of maintaining a perimeter-centric security model in this environment are not hypothetical. The 2020 SolarWinds breach, which affected the US Treasury, State Department, and thousands of private organizations, was executed in part by lateral movement through trusted internal networks - once inside the perimeter, the attacker moved freely for months. The assumption of internal trust was the vulnerability. Zero Trust is the architectural response to that assumption.
Three Principles, Not a Product
Zero Trust is not a product category that you can buy and deploy. It is a security philosophy that manifests in architecture decisions, policy enforcement, and operational practices. The marketing from vendors who sell "Zero Trust solutions" has muddied this point considerably, because the label has become attached to specific products in ways that overstate what any single product can deliver.
The National Institute of Standards and Technology (NIST) defines Zero Trust around three core principles, and understanding them clearly is prerequisite to making good architectural decisions.
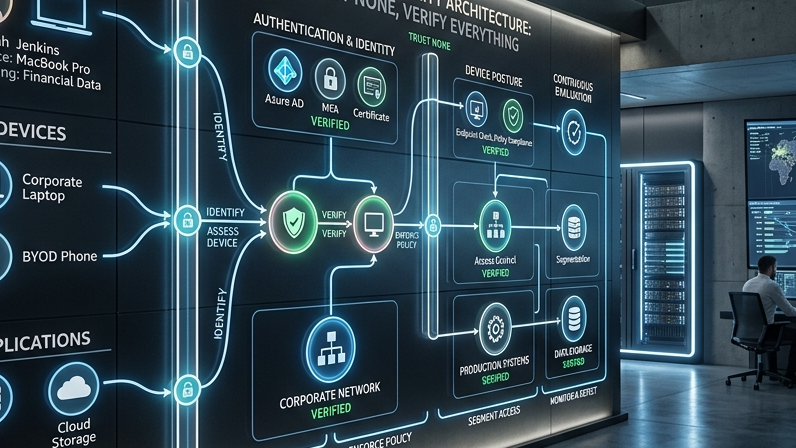
Verify explicitly. Every access request - from any user, any device, to any resource - should be authenticated and authorized using all available signals. This is a departure from the perimeter model where being inside the network was itself a form of authentication. In a Zero Trust architecture, network location grants no privileges. Identity, device health, application context, and behavior signals all contribute to access decisions that are made continuously, not just at login.
Use least-privilege access. Users and workloads should have exactly the permissions required for the task they are performing - no more, no less. This is not a new principle in security, but Zero Trust operationalizes it more rigorously. Just-in-time access (elevating privileges for a specific task, then removing them) and just-enough-access (constraining what resources a service account can reach) are the practical implementations. The objective is to minimize blast radius: if a credential is compromised, the attacker can only access what that credential was permitted to access.
Assume breach. Design your systems as if an attacker already has a foothold inside your network. This means segmenting resources so that compromise of one does not grant access to others, encrypting data in transit and at rest even on internal networks, and investing in detection and response capabilities alongside prevention. Perimeter security is optimized for prevention. Zero Trust is optimized for containment and rapid detection when prevention fails - which, at enterprise scale, it eventually will.

The Architecture Components That Implement These Principles
Translating Zero Trust principles into a working architecture requires specific technical components working together. The components are not new individually - most organizations already have some of them. What changes is how they are integrated and what role network location plays (none) versus identity and device health (everything).
Identity Provider (IdP): The foundation of a Zero Trust architecture. Okta, Azure AD, and Google Workspace are the dominant enterprise choices. The IdP is the authority for user identity, handles authentication (including MFA), and issues tokens that other systems validate. Every access request starts here. If your IdP is down, your users cannot work - which is why high availability architecture for the IdP is not optional.
Device trust: Beyond user identity, Zero Trust requires verifying that the device making the request meets your security baseline. Is it managed by your MDM? Does it have current OS patches? Is the disk encrypted? Is endpoint protection active? Mobile Device Management (MDM) tools like Jamf or Microsoft Intune, combined with Endpoint Detection and Response (EDR) tools, provide the signal. The challenge is enforcing access policies based on device health without creating so much friction that users find workarounds.
Micro-segmentation: Rather than allowing any-to-any communication within a network segment, micro-segmentation defines explicit allow-lists between workloads. A web server can reach the database. The database cannot initiate outbound connections. An HR application can reach the payroll service. Nothing else can. Tools like Illumio and VMware NSX implement network-layer micro-segmentation. Service meshes like Istio implement it at the application layer. Both approaches add operational complexity that needs to be weighed against the security benefit.
Continuous verification: Unlike the perimeter model where authentication happens once at login, Zero Trust systems re-evaluate access continuously. Session tokens have short lifetimes. Anomalous behavior (logging in from Vietnam when the user normally logs in from Singapore, accessing a database at 3am when the user normally works office hours) triggers additional authentication steps or session termination. This is the "assume breach" principle operationalized: you do not trust a session just because it authenticated correctly 8 hours ago.

Zero Trust vs. VPN: An Honest Comparison
VPNs are not inherently insecure. They are a tool that solves a specific problem - creating an encrypted tunnel from a remote device to a network - and they solve that problem reasonably well within their design constraints. The problem is that the problem they solve is the wrong problem for many modern organizations.
When a user connects via VPN, they typically get access to a network segment, not to a specific application. Depending on how the VPN is configured, this may mean access to many resources the user has no legitimate need to reach. In a 2021 study by Zscaler, 76% of security professionals reported that VPN users often have broader access than their role requires. This violates the least-privilege principle and is a direct consequence of VPN architecture: the VPN grants network access, and application access is enforced (if at all) by separate controls that are often inconsistent.
VPNs also create a performance problem at scale. Backhauling traffic through a VPN concentrator creates latency and capacity constraints that become acute when large portions of the workforce are remote. Organizations that ran VPNs for pre-pandemic on-site percentages of 20-30% found them buckling when 80%+ of the workforce went remote in 2020.
Zero Trust Network Access (ZTNA) tools - Zscaler Private Access, Cloudflare Access, Palo Alto Prisma Access - replace the VPN with application-level access control. Users authenticate to the ZTNA proxy, which evaluates their identity and device posture and grants access to specific applications they are authorized for. Traffic routes directly to the application rather than backhauling through a concentrator. The access is scoped, auditable, and revocable at the application level rather than the network level.

Implementation Roadmap: How Organizations Actually Do This
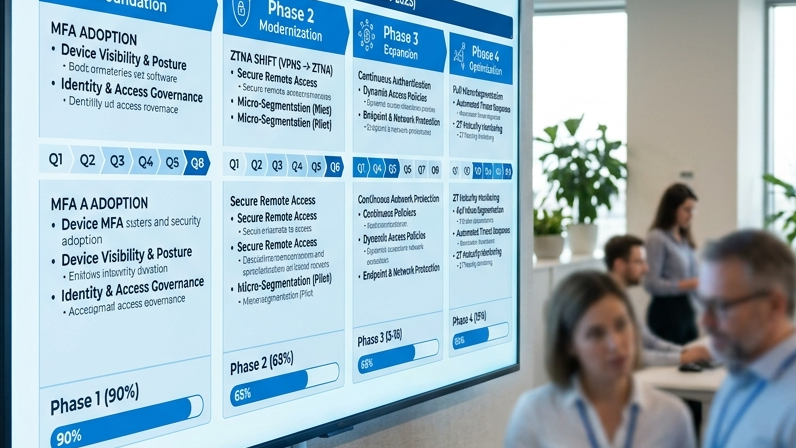
Zero Trust transformation is a multi-year program, not a product deployment. Organizations that have successfully completed meaningful Zero Trust implementations typically follow a phased approach that delivers security improvements at each phase rather than requiring full transformation before realizing any benefit.
Phase 1 - Identity consolidation (3-6 months): Consolidate authentication into a single IdP. Enable MFA universally - not as an optional user preference, but as a hard enforcement policy. Audit service accounts and remove unused credentials. This phase alone closes a significant percentage of common attack vectors. The 2022 Verizon Data Breach Investigations Report found that 80% of breaches involving hacking used compromised credentials.
Phase 2 - Device management (3-6 months): Enroll all endpoints in MDM. Define and enforce device health baselines as a condition of access. Deploy EDR across the fleet. Begin feeding device health signals into access policy decisions. By end of Phase 2, you know that the devices connecting to your systems are managed and meet your security baseline.
Phase 3 - Application access control (6-12 months): Replace VPN with ZTNA for remote access to internal applications. Implement SSO with your IdP across all business applications (this is harder than it sounds - many legacy applications do not support modern SAML/OIDC flows). Start enforcing conditional access policies that consider device health, user behavior, and risk signals.
Phase 4 - Workload segmentation (6-12 months): Apply micro-segmentation to critical workloads. Define explicit allow-lists for service-to-service communication. Implement mutual TLS for internal service traffic. Build the logging and monitoring infrastructure to detect anomalous lateral movement. By end of Phase 4, your environment has meaningfully reduced blast radius for any compromise.
Common Pitfalls: Where Zero Trust Transformations Stall
The failure modes in Zero Trust implementations are well-documented because many organizations have attempted them. Understanding the common pitfalls in advance is the clearest path to avoiding them.
Over-complexity in the initial architecture. Organizations that try to implement the full Zero Trust architecture in a single program often stall because the scope is too large to maintain momentum. The phased approach above works because each phase delivers tangible security improvements that justify continued investment. A single-phase "full Zero Trust transformation" is a multi-year program with no intermediate deliverables, which makes it vulnerable to budget cuts when organizational priorities shift.
User friction that drives workarounds. Zero Trust adds friction to the user experience - MFA prompts, device enrollment requirements, conditional access policies that block unmanaged devices. If the friction is excessive, users find workarounds: forwarding work email to personal accounts, using personal devices to avoid MDM enrollment, sharing credentials to avoid policy-blocked access. These workarounds recreate the security gaps you were trying to close. Getting the user experience right requires input from actual users, not just security teams.
Treating Zero Trust as a one-time project. The access policies that are appropriate today will not be appropriate in 18 months as your business changes, new applications are added, and the threat landscape evolves. Zero Trust requires ongoing operational commitment: policy review cycles, device compliance enforcement, log analysis, and incident response. Organizations that treat it as a project to be completed rather than a practice to be sustained typically see their Zero Trust posture erode within 12-24 months of the initial implementation.
Building Zero Trust with GTEMAS
GTEMAS security practice works with organizations at every stage of Zero Trust maturity - from initial assessment and roadmap development, through technical implementation of specific components, to ongoing managed security operations. Our approach starts with understanding your actual threat model and risk profile rather than assuming a generic framework applies directly to your context.

Zero Trust transformation involves technology decisions that will shape your security architecture for years. Getting the foundational choices right - IdP selection, device management approach, segmentation strategy - matters more than moving quickly on the wrong path. If your organization is evaluating where to start or how to accelerate an existing Zero Trust initiative, we can provide a structured assessment and a realistic implementation roadmap.
